https://archlinux.org/news/the-xz-package-has-been-backdoored/
https://www.openwall.com/lists/oss-security/2024/03/29/4
So update !
Affected Versions:
5.6.0-1
5.6.1-1
Current fixed version is 5.6.1-2
https://archlinux.org/news/the-xz-package-has-been-backdoored/
https://www.openwall.com/lists/oss-security/2024/03/29/4
So update !
Affected Versions:
5.6.0-1
5.6.1-1
Current fixed version is 5.6.1-2
Done. Thanks for the heads up.
p.s. - If in attempting to update (sudo pacman -Syu) you get timeout errors trying to access all of the required updated files it could be stale EOS mirrors in your setup… in which case remember to update mirrors (using EOS Welcome screen can be an easy way to do so.) ![]()
Does anything else need to be done besides running a full update? Only been using Linux for a few months so I want to make sure I don’t leave my PC vulnerable.
I’ve followed the conversation in the original report, and found some users comparing Arch’s xz 5.6.1-1 vs. 5.6.1-2. By disassembling the liblzma library (which is the affected part, as far as I’ve understood), it appears that our packages might have never been affected by the backdoor, due to a deb/rpm check in the script that decides whether to inject the vulnerability or not.
In any case, please update your packages to be on the safe side!
References:
https://www.openwall.com/lists/oss-secu … 4/03/29/17
https://www.openwall.com/lists/oss-secu … 4/03/29/20
https://www.openwall.com/lists/oss-secu … 4/03/29/22
that’s the reason indeed.
Someone on telegram linked this:
Scroll down to his subtitle ‘a sudden push for inclusion’ then the context of the chronology becomes clearer (sinister). this guy Boehs did some excellent sleuthing/chronicling of the pieces. I learned a lot here.
Seems the community reacted swiftly though.
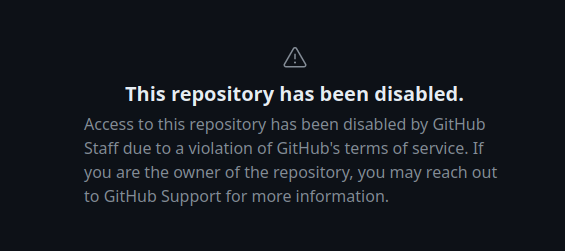
RIP ![]()
They’ve disabled everything! ![]()
I have an official comment on the issue:

Arch isn’t affected by the known backdoor.
From https://security.archlinux.org/ASA-202403-1
Impact
The malicious code path does not exist in the arch version of sshd, as
it does not link to liblzma.However, out of an abundance of caution, we advise users to avoid the
vulnerable code in their system as it is possible it could be triggered
from other, un-identified vectors.
Still as they say, better to update system. There can still be more unknown components that affect the compromised versions.
Edit:
Also mentioned on Arch news page
Arch does not directly link openssh to liblzma, and thus this attack vector is not possible. You can confirm this by issuing the following command:
ldd "$(command -v sshd)"However, out of an abundance of caution, we advise users to remove the malicious code from their system by upgrading either way. This is because other yet-to-be discovered methods to exploit the backdoor could exist.
I really appreciate all of the eyes watching linux here. Even for not “directly specific to Arch” stuff. It’s impressive. Thanks for all of the reading and info. Both of my computers are not compromised. One doesn’t even have xy, and the other is much older and will likely bypass the bad packages upon the next update.
oh boy…
I hope it’s the happy case of “Correlation doesn’t imply causation”…coz
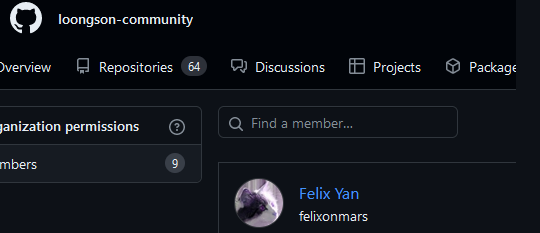
He’s maintainer of absolute most of Arch packages.
P.S. To be fair he’s pretty much inside any chinese project from Deepin to stuff like that.
Indeed he is a trusted member and I bet Chinese so simply no wonder is active in Chinese projects… and very active.
We should not start ![]() hunting.
hunting.
well said… ![]()
Aren’t we?
People are weird.
Whole security world is hunting that malicious guy from xz right now and every project he was ever part of as well as people associated with him (duh, i wonder why?! Could it be because he has injected very sophisticated obfuscated backdoor for more than 2 years).
So it’s natural to find anything that could be affected / connected.
It could be false flag, for all i care…what is important - make sure supply chain / trusted users are not in any way shape or form compromised.
Part of the process of building (false) trust is having non-malicious interaction with reputable sources and communities. Insinuating that an interaction is an association to the malicious outcome is creating a ![]() hunt.
hunt.
I would also assume the opposite is true: The more active someone is in a very popular community project the lesser the chance it’s a bad actor, because that usually requires social interactions bad actors have to avoid.
Well, depends on motivation. xz itself is the proof of that…It’s the most technically complicated way to backdoor a project that is used by all Linux distros in the world.
So far what is pretty clear:
xz project affected, but part of wider operation that assembles and use mechanism of given backdoor, what we know so far is they’ve targeted at least OpenSSH.Regardless, it’s great that it was discovered by just a simple user’s benchmark accident.
Wow, the plot THICKENS!
![]()
I’m not weird. ![]()