Whenever I’ve installed various Linux distros they have always come with the UFW firewall included. I noticed that EndeavourOS does not include this on a default installation and requires downloading post-install. Networking has always been the bane of my life for decades (!) and I’m reluctant to install an OS that does not have a firewall ready before going online. Can someone reassure me that it will be alright to install without a firewall available? Endeavour looks like a great distro! Thanks.
Do you connect your PC directly to the Internet? No, you go via a router, right? Then the firewalling is happening at the point of your router and an ingress-focussed firewall within a LAN is entirely pointless.
There are lots of different firewall solutions available and everyone has their own preference. Like most software, a bare minimum is installed by default and you can choose which you prefer for your own installation.
If ufw is the one you are used to using, you can use that.
Alternatively, ufw is just a management framework for iptables which is built-in to the kernel. Many people since use that directly and it is available on every install.
Personally, I have been using firewalld which is another good option. The choice is left to you.
Thank for the quick reply. Unfortunately the router firmware is pretty ancient. But I did check with GRC: ShieldsUp! and I had a Perfect Stealth Rating (which I understand is pretty cool  I understand) so I’m hoping that will be enough. Can you give me any guidance. Very grateful to you.
I understand) so I’m hoping that will be enough. Can you give me any guidance. Very grateful to you.
For most people, a local firewall is critical component of home security. In the current world where many people have many devices on their network and/or guests on their network, protecting yourself from threats that originate within your network is critical.
Of course, some people live alone and have minimum devices but that is the exception more than the rule these days.
Came here to second firewalld. I find the zones feature quite useful on laptop devices. It integrates with NetworkManager, so the zone in use can be set at the network level. Also, “Shields Up” (in the applet) looks like it could potentially be quite a useful feature for limiting outbound traffic during VPN usage, but I haven’t tried configuring this yet.
The only negative I’ve found with firewalld so far is that the selection of pre-configured services is quite limited. UFW is much more expansive in this regard. For instance, I had to make my own custom service for the minecraft server on my pi. It’s not that hard to do though. Also, you can just allow specific ports instead.
Not meaning to hijack the thread; Only a quick question:
Running the test at GRC: ShieldsUp! I get the following result:
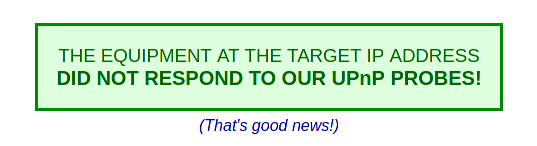
Does the “good news” mean that my network is protected? I was using a VPN connection at the moment of the testing.
@Gren
Not favouring a specific firewall over another or debating about its efficacy. If you want a specific package to be “pre-installed” on your new system (like ufw), it’s possible to do so.
Here is a link to wiki page, which also has a video about the process.
We haven’t firewall enabled by default but we do provide a shortcut to enable it on the welcome app:
They may have the ufw package installed, but is it enabled and configured? Without firewall rules ufw does nothing.
Firewall rules are specific and depend heavily on how a system is used, you would have to create these yourself on any distro I would imagine, not just EndOS.
It means your network didn’t respond to UPnP probes which is a good thing. Protecting a network is much more involved than just that one thing.
That’s not quite the same thing as protection against online threats, and I’d honestly be pretty concerned about a home network that was “untrusted”. How would you share media etc. if you had people attacking your PCs?
However, my original point was that ingress from the Internet is prevented by the router; computers on the wider Internet don’t have direct access to a PC running on a LAN, therefore having a local firewall to prevent ingress from those systems is actually doing nothing.
In addition, a firewall only helps protect running services, and Arch-based systems have no publicly-accessible services running by default. So, without any running services a firewall blocking ingress is not actually doing anything useful.
Id argue that if your home network is this unsafe a firewall is just a bandaid for ignorance and poor practice. Especially when it comes to guest in your home having a completely separate Guest network setup on your router is a good idea so you dont compromise your actual lan.
That said firewall setup on linux for someone who isnt knowledgeable enough to at least have a decent network setup is probably a bit outside that persons ballpark for the moment and should focus on securing their network first. Thats just imo and if someone wants to still add one on their machine thats fine too, doesnt hurt necessarily.
Thats a very good point, on default to my knowledge many Distros dont tend to expose services and ports in the same fashion and Windows does
A few years ago, I would have agreed with you but the world has changed.
Things common on a home network now that weren’t in the past
- Smart devices - TVs/thermostats/toasters/major applicances/wearables/cameras/doorbells/locks/etc. It isn’t uncommon for a home network to have 20-30 of these devices and many of them never get patched
- More devices - People just generally have more computing devices than in the past. Phones/tablets/laptops/PCs/etc. I remember when my family used to share a computer, now everyone has multiple computing devices.
- Service-side compromises - This is increasingly a real issue. It doesn’t matter how good your edge protection is if the compromise if pulled from the inside out.
- Devices which by default helpfully share wi-fi passwords so guests can easily access our network.
- Other users of our home network who aren’t as sophisticated as us who do stupid things.(This one probably isn’t new
 )
)
Because it is easier to compromise a home network than ever before. Having local firewalls is well worth the minimal investment it takes to install, configure and maintain them.
Of course, if you have iron-clad control of your home network and/or a tiny network the story is different. However, very few people have tiny networks these days and if you have a bullet-proof network you are sophisticated enough that you don’t need my advice. ![]()
If you are an unsophisticated user, it is pretty easy to start services without recognizing the security impact of doing so.
I’ve noticed that many ‘expert’ Linuxes do not come with firewalls included in the install ISO (I know iptables is always included and is the ‘real’ firewall), so I trust the experts that they know what they are doing, but I just wanted to make sure. I wanted to enable a firewall before attaching the computer to the internet and I’m used to UFW, so if I can enable it on the Welcome app, as Bryanpwo states or add it to packages to installed, as Flyingcakes says, I am happy with both of those solutions. I’d be interested in any other opinions though. Thanks.
If you like ufw, I would use that. If you enjoy trying new things, try firewalld. Those two are probably the most widely used solutions at this point.
The Welcome app button can install gufw but it does not enable it by default.
User must manually start the ufw service using the info from the link by @Bryanpwo and set appropriate profile and rules e.g. with gufw.
It’s also easy to use a firewall to prevent printing and sharing files with your Android phone. ![]()
But yes, still a lot of valid points, as I’ve come to expect. ![]()
It’s kind of a weird halfway house for firewalls on Arch at the moment. Arch is heading down the systemd route. systemd lists iptables as a dependency, so you can’t easily get rid of it. systemd is developed by the Red Hat team, who are also developing firewalld. However, firewalld depends on nftables, not iptables.