Is there any way to encrypt only home directory in such way that it would be decrypted automatically after login?
If I understand what you are proposing, I don’t know of a way to do that but if you could it would be totally insecure.
It is trivially easy to change a users password on an unencrypted drive. So all an attacker would have to do is change your password and then login.
There is a way, using systemd-homed, but it is not commonly used yet, and thus you "ll have to read a lot and configure it yourself for your requirements.
https://wiki.archlinux.org/title/Systemd-homed
https://man.archlinux.org/man/homectl.1
https://man.archlinux.org/man/systemd-homed.8
That is true systemd-homed stores that information in the home directory.
This worked fine in archinstall (but it had other problems) with separate home partition just fine (used same password as for user), but if I modify partitionLayout to have separate home, it will encrypt all by default. Manual partitioning is not an option as it still requires entering password 2 times. I have old SSD with such an install, it shows that root partition is f2fs and home is encrypted. But I don’t remember having to each time enter password before login prompt.
Also changing password shouldn’t give attacker access to my files. Well, at least similar setup with Mint encrypts everything with master key and uses password to encrypt it, so decryption at login works just fine.
No idea tho if Mint installer and archinstall did the same thing, but presumably
Why don’t you want to encrypt the entire drive?
Because it forces me to first enter encryption password and then user password (even if they’re the same). I can’t get to grub menu without password because of that.
So what happens when you change your password? Does it fail to unlock /home because the password on the encryption is different? If so, it may be a pam module doing the decryption.
If it works the way you want on Mint, you could spin up Mint in a VM and look at what it is doing. There would be two things to check. What is it using to encrypt the partition and how is it unlocking it? The former can be seen just by looking at the partitions. The latter might take some digging but I would start by looking at what pam modules are in use.
It isn’t essential that you deal with your home partition during the install. You could not setup a separate home partition but leave some empty space on the disk for it. Then set the partition and the encryption up however you want after installation.
Well a naive way to get around this would be to store your encryption key on a usb (or one of those hardware keys e.g. Yubico keys) and configure the initramfs and bootloader (I think?) to unlock your drive as soon as it gets access to the key, without prompting for a password.
I haven’t ever changed password, but probably the master key would be just reencrypted with new password.
Seems that Mint used ecryptfs, while archinstall created separate encrypted home partition (mounting it requires password on PC if I boot from other drive, but I don’t remember to enter password before login prompt). However, when I tried to get the same with Calamares (manual partitioning with /home encrypted), it would ask me to enter password before login prompt (but after grub).
While this is possible, it doesn’t seem likely to me. Also, since it is trivially easy to change a password without the old password, this would make the encryption fairly useless unless Mint is not handling username/passwords in a traditional manner. However, I suspect/hope that it doesn’t work that way and if you changed your password it would fail to unlock the encryption automatically. I would be curious to test it but I have no free time today unfortunately.
Calamares doesn’t support what you are wanting. However, as explained above, it doesn’t have to be done at install time, it can be done manually post-install.
I actually meant that one would have to know the password to change it. So yes, if password was changed without somehow typing the old one, it would fail to decrypt.
Great. Is there any good arch installer which can finally just work fine without strange errors and with all necessary features?
Archinstall, for example, fails to set up keyboard layouts properly (well, at least with Cinnamon) and few other details. Calamares can’t properly setup encryption and installs garbage like firewalld which silently breaks qrcp.
That isn’t how password changing works.
Your definition of a good installer seems to be one that works exactly as you prefer and installs only what you like.
I don’t think you are going to find that unless you make it yourself.
What would be the perfect installer.
Guess I’ll have setup encryption after install. Are there any instructions for that? Still don’t understand why archinstall did a better job than Calamares in regards to encryption.
With manual partitioning, I had to type password before login prompt. Is there any way to make it decrypt automatically after login? Maybe this would be easier than setting up encryption from scratch .
I tested a lot of installers, the best one with full control is manual “arch way” lol!
But, for me, the easiest with good control of encryption is from archlabs
To my surprise it was easy and painless to convert to systemd-homed.
You can use ecryptfs to do it, and it’s possible to do it at any time:
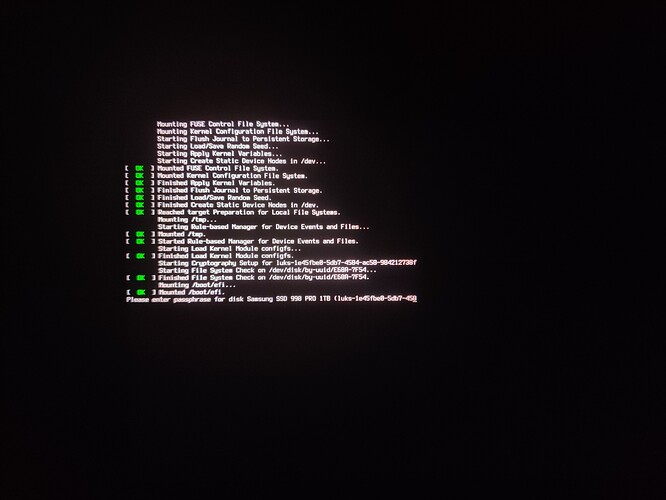
Still can’t solve this. After grub I see this:
After entering password it shows KDE login prompt and I have to type password for the second time.
Can I make it show me only KDE login prompt and don’t ask password 2 times? Tried pam_mount without any success.
What did you do to get to that point? Did you use encryptfs or something else?
Did you remove it from /etc/fstab and rebuild your initrams?
Manual partitioning in installer (f2fs / unencrypted and f2fs /home encrypted with same password as user). After that I installed pam_mount (according to arch wiki) and nothing changed. Still same password prompt as before.
Also Cinnamon installation seems broken. It seems not to have English keyboard layout on login screen and therefore one can’t login at all to change that.
TBH ecryptfs is quite a mess to install. It seems to work right now, but it’s too much hustle. Not very keen on using it next time. Maybe if Calamares supported it, it might’ve been actually usable.