Keep in mind that:
It won’t block anything coming from the Internet, only if you have a portforward in router router/gateway.
In case you decide to forward something to your PC, you would have to create a portforward in your gateway and then create a policy in the FirewallD.
This is specially useful for people that are always connecting to strange networks… You don’t want the guy in the table near to you, or in the room of the hotel near to yours trying to access your SSH port and etc…
There are things we can control, and others we cannot.
In case of these public wifi networks, there is an option to isolate devices so they can’t speak to each other, this is something we can’t control, its defined by the network administrator.
In case you don’t trust anyone in that WIFI network, not even the administrator, you could just use a VPN…
Not speaking about VPN providers here, you can connect to your own VPN service hosted in your house and use the Internet from there…
The VPN would make sure that if you connect to a fake SSID, get an IP from a rogue DHCP server, or even an ARP poisoning attack in which people becomes the gateway (all of these can be categorized as a MITM attack), your data would be protected because everything is encrypted.
What you need to know is that a firewall is not perfect, the user must be aware as well.
There are bad network administrators, and most of all, there are bad people out there.
In my situation:
I have a desktop, so I’m not connecting to strange networks, only my home network.
My router/gateway is a firewall in which I have policies in place, no portforwards what so ever…
My network is divided in VLANs, and my PC is in a different VLAN than the other devices are, LAN in which my PC is, the WIFI and the GUEST vlans.
All these VLANs have their own rules, LAN can speak to everyone, WIFI and GUEST networks can go only to the Internet and nothing else.
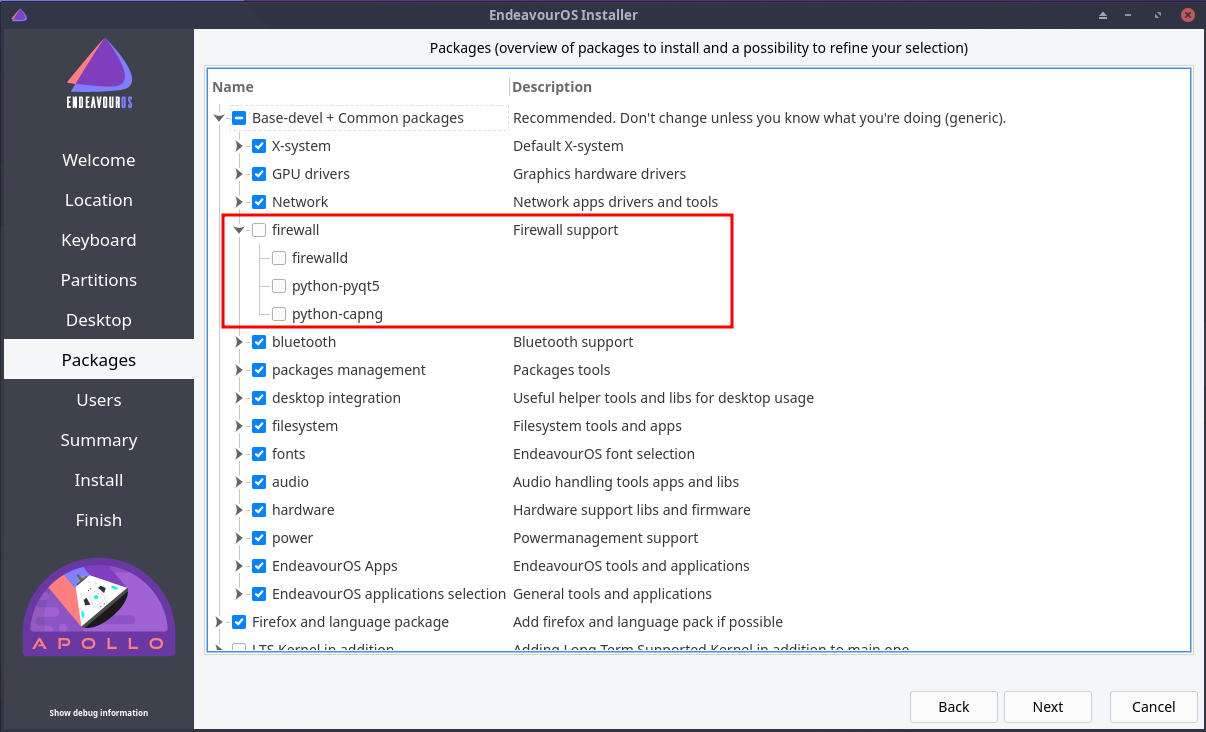
Also, I’m not a big fan of zone based firewalls, so I decided to disable it.